-
What Is Oracle RMAN Encrypted Backup?
-
Why Use Encryption with RMAN Backups
-
How to Create Encrypted Backups with Password Encryption?
-
How to Use Transparent Encryption for RMAN Backups?
-
Dual-Mode Encryption: Combining Flexibility and Security
-
How to Restore Data from Encrypted Backups?
-
How Vinchin Backup & Recovery Strengthens Your Oracle Backup Strategy
-
Oracle RMAN Encrypted Backup FAQs
-
Conclusion
Imagine this: your team ships backup tapes offsite or stores copies in cloud storage you do not fully control. What if someone intercepts those files? With sensitive business data at stake, even one lost backup can lead to disaster. Oracle RMAN encrypted backup helps you avoid this risk by securing your backups against unauthorized access—no matter where they end up.
This article explains what Oracle RMAN encrypted backup is, why it matters for modern IT operations teams, and how you can set it up step by step at beginner through advanced levels. You’ll also learn how to restore encrypted backups and see how Vinchin can make your Oracle backup strategy even stronger.
What Is Oracle RMAN Encrypted Backup?
Oracle Recovery Manager (RMAN) encrypted backup is a feature that encrypts your database backups as they are created—not after the fact—so data never leaves your system unprotected during transfer or storage. Both backup sets and image copies can be encrypted using this method.
When enabled, RMAN writes all selected data into an encrypted format directly on disk or tape. Only users who possess the correct keys or passwords can decrypt these files during recovery operations; others cannot read any information from them.
RMAN supports three main modes:
Password-based encryption: Requires a password each time you back up or restore data.
Transparent encryption: Uses an Oracle wallet (keystore) so no manual password entry is needed once configured.
Dual-mode encryption: Combines both methods for flexibility—you can restore using either a wallet or a password.
Encryption happens inline as part of the I/O stream during backup creation rather than as an extra processing step afterward. This design makes it efficient and secure for enterprise environments.
Why Use Encryption with RMAN Backups
Encrypting your RMAN backups is about more than just meeting compliance checklists—it’s about building true defense-in-depth for your organization’s most valuable asset: its data.
Backups often leave the safety of your primary environment when stored offsite or in third-party clouds where physical controls are limited or absent altogether. If these files are not protected by strong encryption, anyone who gains access could recover sensitive business records without restriction.
Encryption ensures only authorized personnel—those holding valid keys or passwords—can ever restore these backups successfully. It also helps satisfy regulatory requirements like GDPR or HIPAA by enforcing strict access controls over archived information.
Think about it: would you leave your server room unlocked? Then why risk leaving unencrypted backups exposed?
How to Create Encrypted Backups with Password Encryption?
Password-based encryption gives you control when moving backups between sites or sharing them across teams lacking access to an Oracle wallet. Here’s how it works:
First, remember that setting password-based encryption applies only within each active RMAN session—you must repeat these steps every time you start a new session requiring password protection.
To create a password-encrypted backup:
1. Start RMAN and connect to your target database.
2. Set session-level password-based encryption:
SET ENCRYPTION ON IDENTIFIED BY 'your_password' ONLY;
The ONLY keyword enforces exclusive use of this password—even if transparent (wallet) settings exist—for all subsequent commands in this session until changed or cleared.
3. Run your desired backup command:
BACKUP DATABASE;
When restoring from such a backup:
1. Start RMAN and connect again to your target database instance.
2. Enter the decryption password before issuing any restore commands:
SET DECRYPTION IDENTIFIED BY 'your_password';
3. Restore as usual:
RESTORE DATABASE; RECOVER DATABASE;
If you lose this password—or forget which one was used—the corresponding backups become unrecoverable forever! Always store passwords securely using approved enterprise tools such as privileged access managers or dedicated vault solutions.
How to Use Transparent Encryption for RMAN Backups?
Transparent encryption automates protection for routine daily backups in trusted environments by leveraging an Oracle wallet—a secure keystore file storing cryptographic keys outside the database itself.
There are two main types of wallets:
Password-protected wallets (
ewallet.p12) require manual opening after restarts but offer higher security if filesystem access is tightly controlled.Auto-login wallets (
cwallet.sso) allow automatic key loading at startup but may be less secure if someone gains OS-level access to their location—a trade-off between convenience and risk every admin should weigh carefully.
Before running any encrypted backups transparently:
1. Configure wallet location in sqlnet.ora, such as:
ENCRYPTION_WALLET_LOCATION = (SOURCE = (METHOD = FILE) (METHOD_DATA = (DIRECTORY = /path/to/wallet) ) )
2. Connect as SYSDBA via SQL*Plus; create/open the wallet:
ALTER SYSTEM SET ENCRYPTION KEY IDENTIFIED BY 'wallet_password';
To reopen after restart:
ALTER SYSTEM SET ENCRYPTION WALLET OPEN IDENTIFIED BY 'wallet_password';
3. In RMAN, configure persistent default settings:
CONFIGURE ENCRYPTION FOR DATABASE ON; CONFIGURE ENCRYPTION ALGORITHM 'AES256';
4. Verify configuration before first use by running:
SHOW ENCRYPTION ALGORITHM;
5. Run regular backup commands without specifying passwords—they inherit settings automatically:
BACKUP DATABASE;
During restores from transparently encrypted sets:
Ensure the correct wallet file exists on disk
Open it if required before starting recovery
If using auto-login (
cwallet.sso), decryption proceeds automatically; otherwise open manually with SQL*Plus first
Losing access to this wallet means losing every associated encrypted backup forever! Treat wallets as single points of failure: always back them up separately from both databases and their corresponding encrypted files—and never store both together.
Dual-Mode Encryption: Combining Flexibility and Security
Dual-mode encryption lets you protect critical databases while maximizing operational flexibility—ideal when teams need options during disaster recovery scenarios involving lost credentials or changing staff roles over time.
With dual-mode enabled, either possession of the original Oracle wallet or knowledge of a designated decryption password allows successful restoration—whichever is available at recovery time suffices!
To set up dual-mode:
1. Start RMAN; connect to target database
2a.If transparent mode already configured:
Issue instead—
SET ENCRYPTION ON IDENTIFIED BY 'dual_mode_password';
(Do NOT include ONLY; omitting it enables dual-mode)
2b.If configuring afresh:
First configure transparent mode per above steps
Then issue same command above without ONLY
3.Run normal BACKUP commands; resulting sets are now accessible via either method
Restoring requires supplying either valid decryption credentials (SET DECRYPTION IDENTIFIED BY ...) or ensuring proper wallet availability/open status prior to issuing RESTORE commands
Remember: Losing both means permanent loss! Document procedures clearly so future admins know which credentials unlock which archives—and rotate passwords/wallets regularly according to policy guidelines.
How to Restore Data from Encrypted Backups?
Restoration procedures depend on which type(s) of encryption were used originally—but always start by confirming necessary credentials are present before attempting recovery!
For transparently-encrypted sets:
1.Open required wallet(s) via SQL*Plus beforehand
2.Initiate standard restore/recover sequence within RMAN
RESTORE DATABASE; RECOVER DATABASE;
For password-protected sets:
1.Set correct decryption phrase within current session
SET DECRYPTION IDENTIFIED BY 'your_password';
2.Proceed with normal RESTORE/RECOVER commands
If dual-mode was used previously then either approach works independently—as long as one credential remains available!
Troubleshooting tip: If RESTORE fails due to missing keys/passwords check that 1) For passwords—the SET DECRYPTION command was issued first in same session; 2) For wallets—that they’re open/readable under current OS user context (V$ENCRYPTION_WALLET view helps confirm status).
Never attempt repeated restores without verifying credential health first—doing so risks accidental lockouts due to failed attempts!
How Vinchin Backup & Recovery Strengthens Your Oracle Backup Strategy
Beyond native tools, organizations seeking streamlined enterprise-grade protection should consider Vinchin Backup & Recovery—a professional solution supporting mainstream databases including Oracle, MySQL, SQL Server, MariaDB, PostgreSQL, PostgresPro, and TiDB. Vinchin Backup & Recovery delivers features such as incremental backup, advanced source-side compression, batch database backup management, granular retention policies including GFS retention policy, and robust storage protection—all designed for reliability and efficiency across large-scale deployments while reducing administrative overhead through automation and intelligent scheduling capabilities.
The intuitive web console makes safeguarding an Oracle database simple:
Step 1—Select the Oracle database to back up;
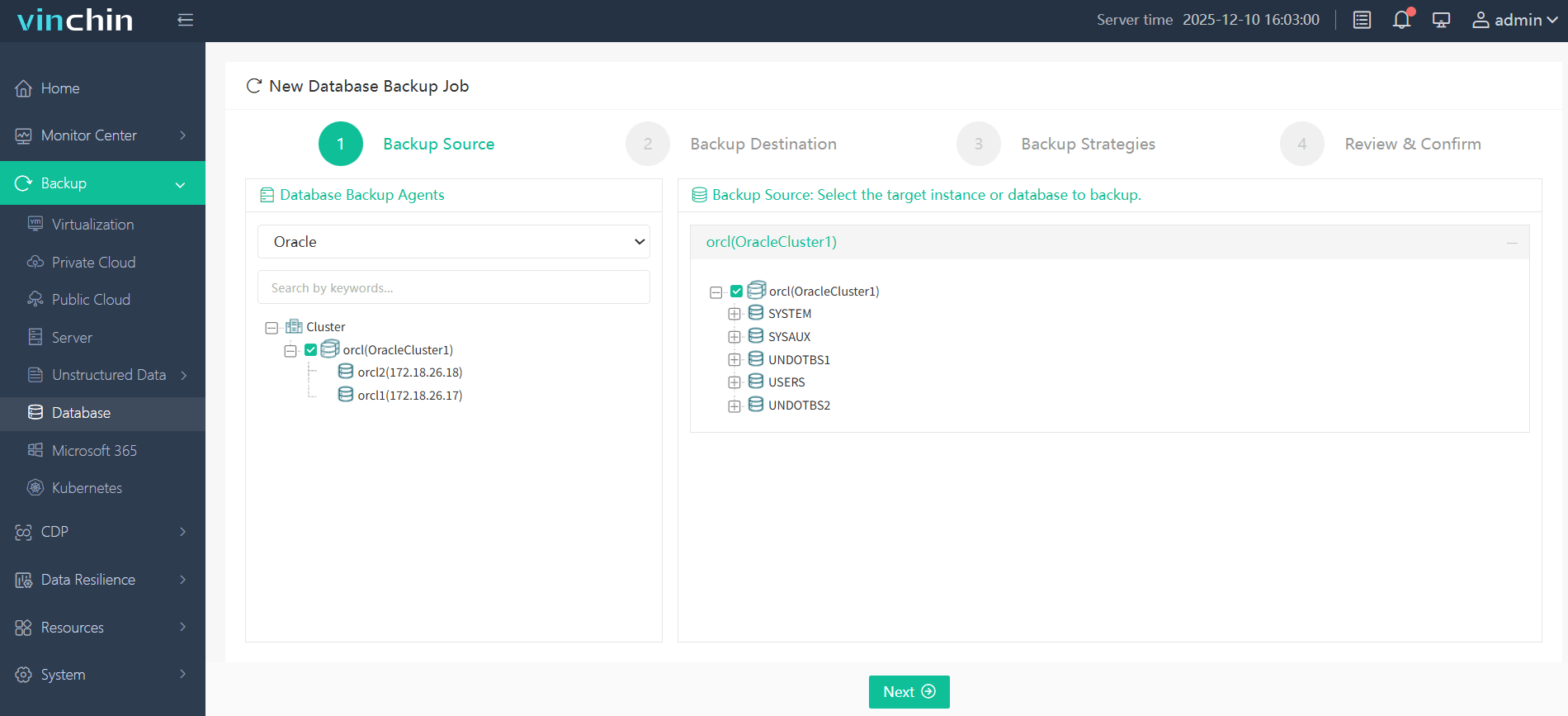
Step 2—Choose the destination storage;
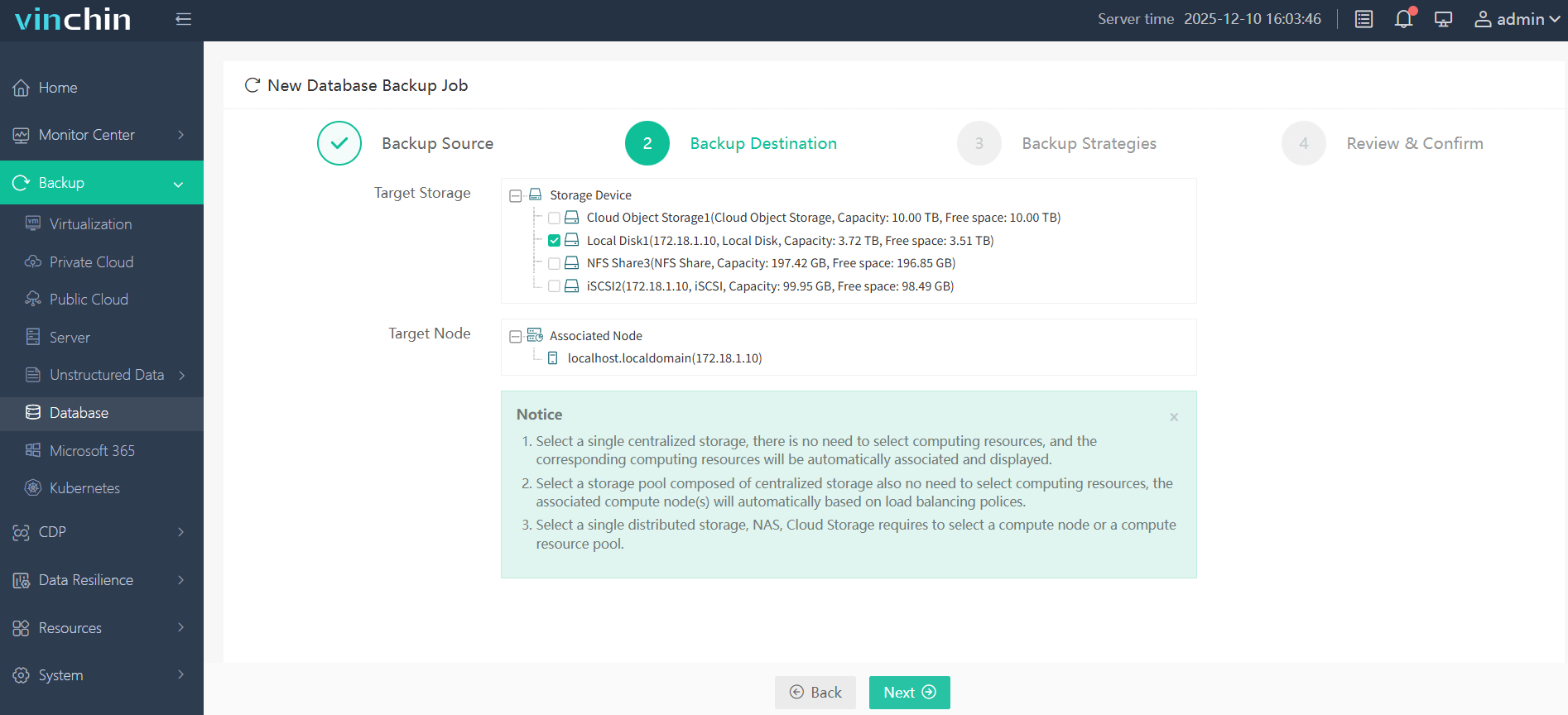
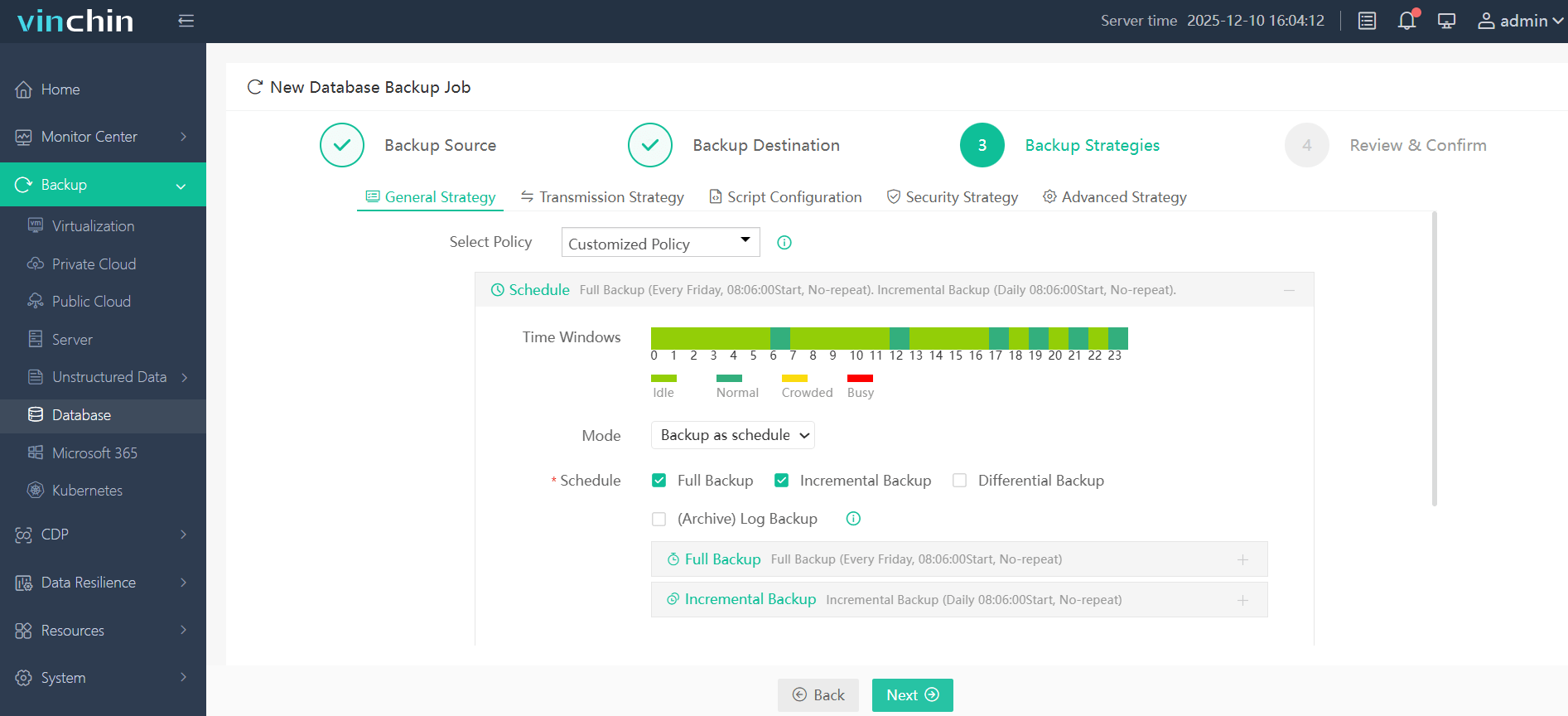
Step 3—Define detailed strategies including schedules and retention rules;
Step 4—Submit the job for execution.
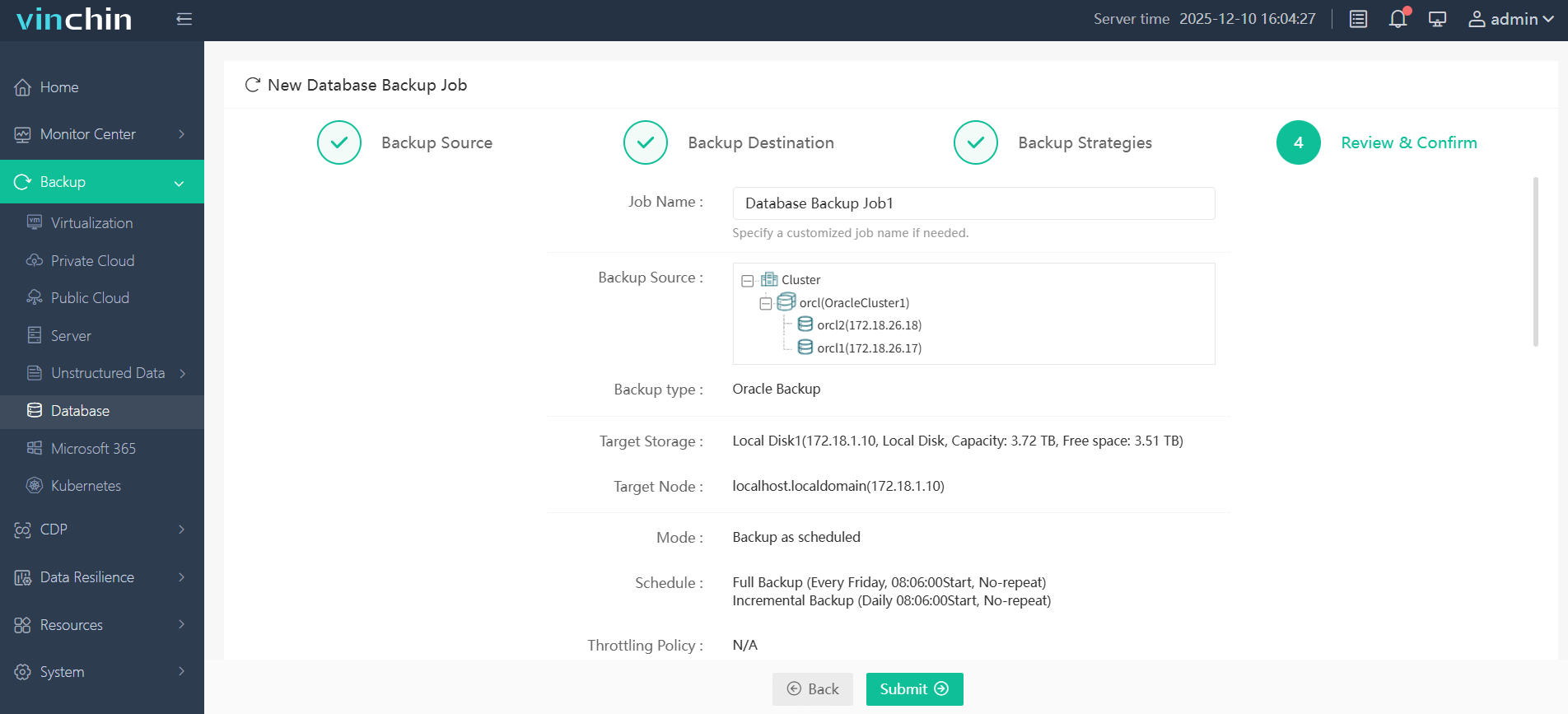
Trusted worldwide by enterprises seeking top-rated data protection software—with thousands of customers globally—Vinchin Backup & Recovery offers a 60-day full-featured free trial so you can evaluate its benefits firsthand.
Oracle RMAN Encrypted Backup FAQs
Q1: How do I check if my latest RMAN backups were actually encrypted?
A1: Query SELECT ENCRYPTED FROM V$BACKUP_PIECE WHERE COMPLETION_TIME > SYSDATE - N; replacing N with days since last check—look for ‘YES’ results only.
Q2: What should I do if my restore fails due to missing decryption credentials?
A2: Confirm you've opened required wallets via SQL*Plus—or issued SET DECRYPTION IDENTIFIED BY ... before running RESTORE in same session; retry after correcting inputs.
Q3: Does enabling encryption slow down my nightly full/differential jobs?
A3: Some CPU overhead occurs but modern hardware minimizes impact; test performance using different algorithms (AES128, AES256) then choose balance fitting workload needs.
Conclusion
Encrypting your Oracle RMAN backups protects business-critical data against theft while supporting compliance goals across industries worldwide—including yours! With careful planning plus strong tools like Vinchin managing day-to-day operations becomes safer—and easier—than ever before.
Share on: