-
What Is Ransomware?
-
Main Types of Ransomware
-
How Ransomware Work
-
How Ransomware Spread: Common Attack Vectors
-
How to Protect Data from Ransomware With Vinchin Backup & Recovery?
-
Types of Ransomware FAQs
-
Conclusion
Ransomware is one of today’s most disruptive cyber threats to organizations worldwide. It can lock you out of your systems, encrypt your data, or threaten to leak sensitive information—all while demanding payment for relief. But did you know there are different types of ransomware? Each uses unique tactics to achieve its goals. Understanding these types is the first step toward building a resilient defense strategy against them.
What Is Ransomware?
Ransomware is malicious software designed to block access to your data or systems until you pay a ransom—usually in cryptocurrency for anonymity. Attackers often target businesses, government agencies, healthcare providers, and even critical infrastructure operators. Paying does not guarantee recovery; sometimes attackers vanish after receiving funds or demand more money later.
The impact can be severe: downtime, lost revenue, regulatory fines, reputational damage—and sometimes permanent loss of data if backups are missing or compromised.
Main Types of Ransomware
Ransomware comes in several forms with distinct methods and risks. Let’s break down the main types you’re likely to encounter as an IT administrator:
Crypto Ransomware (Encryptors):
This type encrypts files on infected systems using strong algorithms like AES or RSA. Victims see a ransom note demanding payment for a decryption key—without which files remain unreadable. Crypto ransomware spreads through phishing emails with malicious attachments or links exploiting unpatched vulnerabilities.
Locker Ransomware:
Locker ransomware locks users out from their entire system interface—desktop, applications, even keyboard shortcuts—while leaving files untouched underneath. A full-screen ransom message blocks all activity except following payment instructions within a set deadline.
Scareware:
Scareware bombards users with fake warnings about viruses or illegal activity on their device. It urges immediate action—often buying bogus security software—or threatens legal consequences if ignored. Some scareware only annoys; others may install additional malware if prompts are followed.
Doxware (Leakware):
Doxware goes beyond encryption by stealing sensitive files before locking devices down—a double extortion tactic now common among sophisticated groups. Attackers threaten public exposure unless paid quickly—a nightmare scenario for organizations handling regulated data like health records or trade secrets.
Ransomware-as-a-Service (RaaS):
With RaaS platforms on the dark web, anyone—even without technical skills—can rent ready-made ransomware kits complete with dashboards and payment portals in exchange for profit-sharing with developers. This model has fueled an explosion in attack frequency and variety over recent years.
Emerging Ransomware Trends
The threat landscape keeps evolving as attackers adapt their tactics:
Double Extortion Attacks: Modern campaigns often combine file encryption with threats to leak stolen data online if ransoms go unpaid—a trend seen in high-profile breaches across healthcare and manufacturing sectors.
Mobile Device Targeting: Mobile ransomware infects smartphones via malicious apps or SMS phishing (“smishing”), locking screens or encrypting photos until victims pay up.
Fileless Ransomware: Some strains operate entirely in memory without writing files to disk—making detection harder for traditional antivirus tools.
Supply Chain Attacks: Attackers compromise trusted software vendors’ updates to distribute ransomware widely—as seen in incidents affecting managed service providers (MSPs).
Staying informed about these trends helps anticipate new risks before they hit your environment.
How Ransomware Work
Each type uses different tactics—but all aim to extort money from victims while causing maximum disruption along the way:
Crypto ransomware typically arrives through phishing emails containing weaponized attachments (.zip/.docx) or links leading to exploit kits hosted on compromised websites. Once inside your network:
It scans mapped drives—including cloud shares—for valuable files
Encrypts them using robust cryptography
Drops ransom notes into affected folders
Attackers may also delete shadow copies to prevent easy restoration from local backups.
Locker ransomware often spreads via drive-by downloads when users visit booby-trapped sites running outdated browsers/plugins—or through infected USB drives plugged into endpoints:
The malware disables user input except mouse clicks needed for payment
System functions remain inaccessible until ransom demands are met
Scareware relies heavily on social engineering:
Pop-up windows claim urgent issues (“Your PC is infected!”)
Users are pressured into purchasing fake solutions—or risk further infection by clicking unsafe links
Doxware attacks start by exfiltrating confidential documents before deploying encryption payloads:
Threat actors contact victims directly with samples proving they possess sensitive data
They threaten public leaks unless paid swiftly—a tactic that increases pressure compared to classic crypto-only attacks
RaaS enables rapid deployment at scale:
Affiliates sign up anonymously online
Developers supply customizable payloads plus support services
Profits split between parties based on successful infections
Detection and Early Warning Signs
Early detection can make all the difference during an active attack:
Look out for sudden spikes in CPU usage as mass file encryption begins—or unexplained changes in file extensions across shared drives.
Monitor logs closely: repeated failed login attempts may signal brute-force efforts preceding deployment.
Unusual outbound traffic patterns—to unfamiliar IP addresses—could indicate command-and-control communications.
Frequent creation/deletion/modification events within short timeframes should trigger alerts from endpoint detection tools.
If users report locked screens displaying countdown timers—or discover ransom notes scattered across directories—it’s time to act fast!
Proactive monitoring combined with automated alerting gives admins precious minutes needed to contain outbreaks before widespread damage occurs.
How Ransomware Spread: Common Attack Vectors
Understanding how different types spread helps strengthen defenses:
Phishing remains the top entry point—with attackers crafting convincing emails impersonating trusted contacts or brands.
Remote Desktop Protocol (RDP) brute-forcing targets exposed servers lacking multi-factor authentication; weak passwords make this vector especially risky.
Software supply chain compromises inject malware into legitimate update packages distributed by reputable vendors—a growing concern highlighted by recent global incidents.
Removable media like USB sticks still pose risks when plugged into unsecured machines; disabling autorun features reduces exposure here.
Drive-by downloads exploit browser/plugin vulnerabilities when visiting compromised sites—even without clicking anything suspicious!
Regularly reviewing these vectors ensures layered protection stays effective against evolving threats targeting every organization size—from small businesses up through large enterprises.
How to Protect Data from Ransomware With Vinchin Backup & Recovery?
Vinchin Backup & Recovery offers a much simpler and more efficient cloud backup service. Vinchin's cloud backup not only comes with robust security features such as real-time monitoring technology and encrypted data transmission to ensure the security of the backup process, but its system is also very easy to install and manage without the need for additional hardware or complex configurations.
Additionally, Vinchin supports the 3-2-1 backup strategy, ensuring that business data is backed up on multiple types of storage media, with at least one copy stored offsite. Even if local storage is affected by a ransomware attack, the cloud backup copy ensures that data remains secure and recoverable.
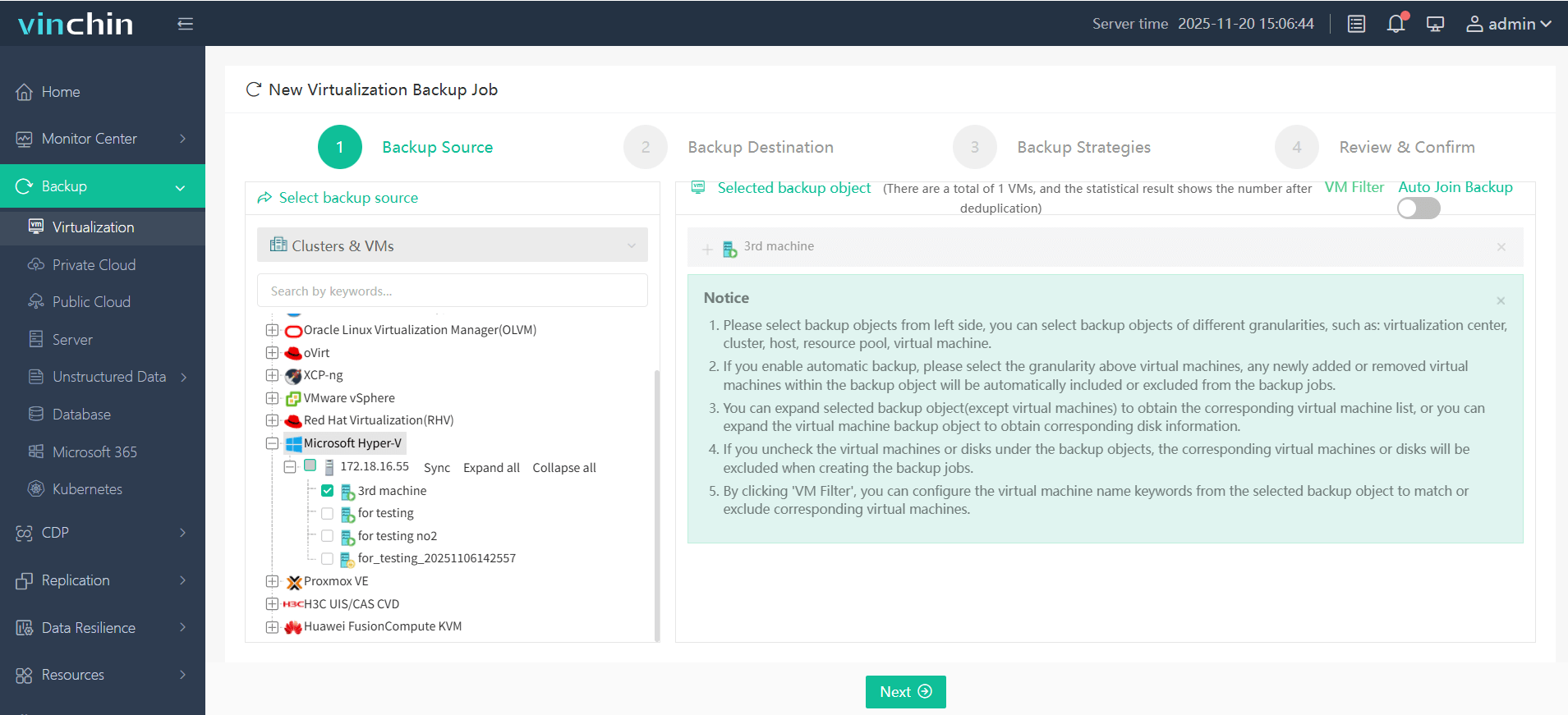
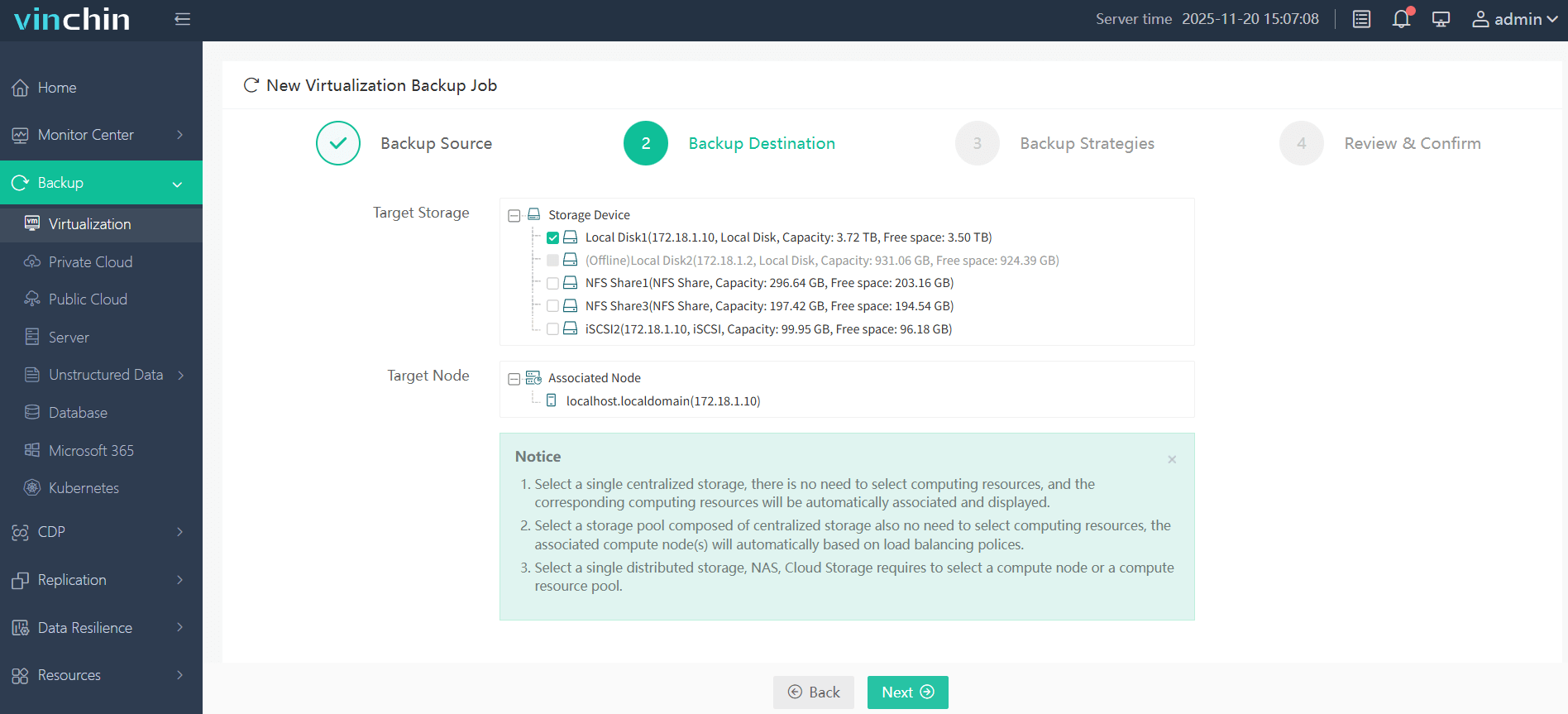
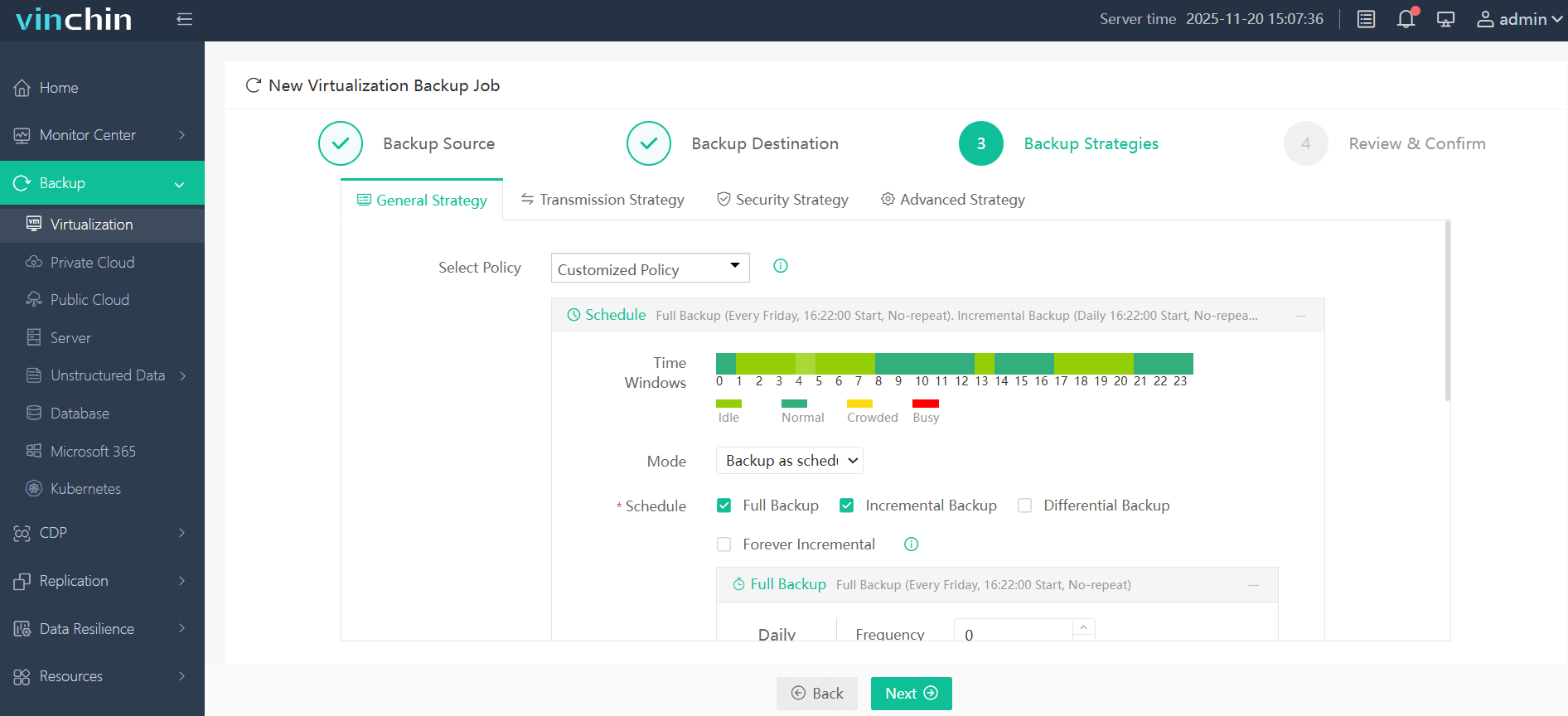
The web console of Vinchin Backup & Recovery is extremely intuitive: backing up critical assets typically involves just four steps tailored for each environment—for example:
Step 1. Select the VM to back up
Step 2. Choose the desired backup destination
Step 3. Define scheduling/compression/throttling strategies
Step 4. Submit the job
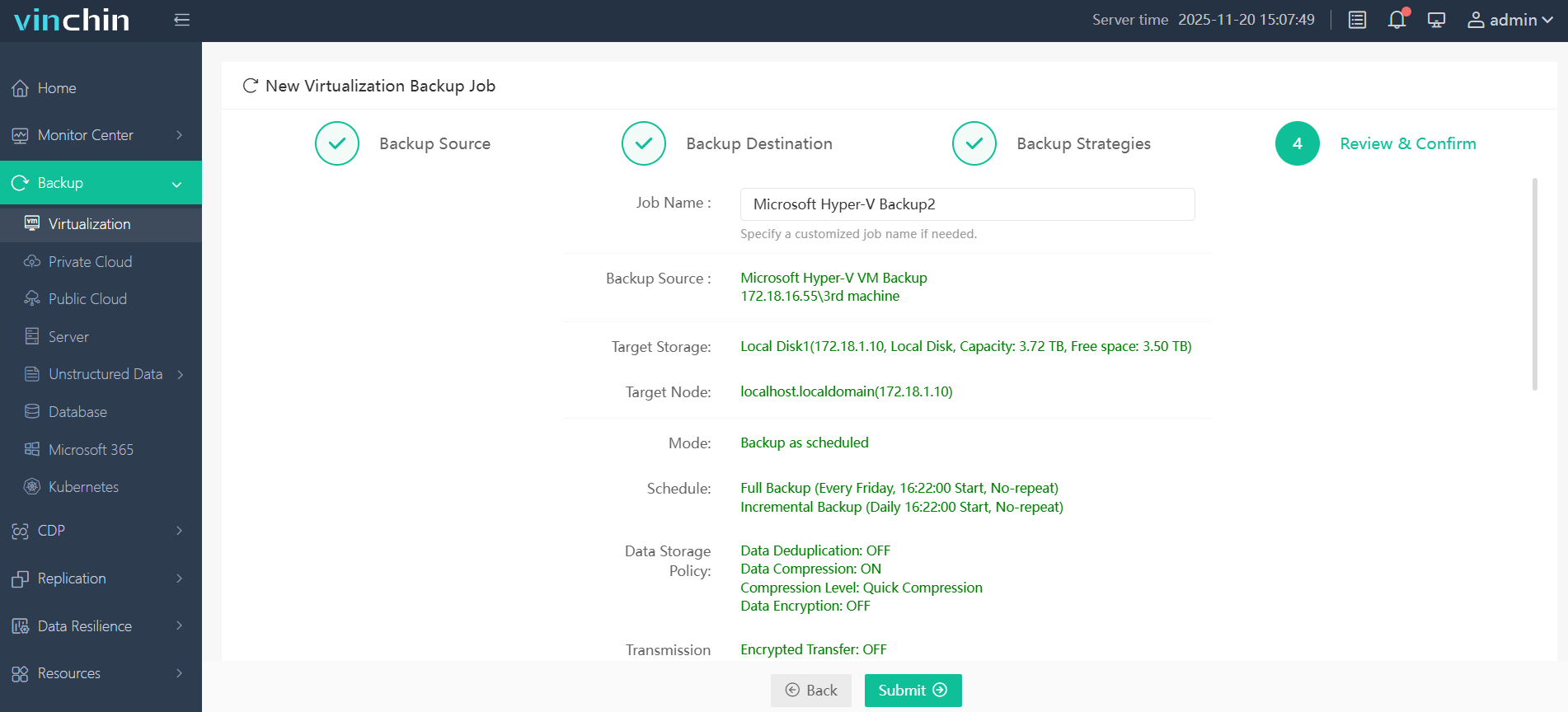
Trusted globally by thousands of enterprises with top ratings in independent reviews, Vinchin Backup & Recovery offers a fully featured free trial valid for 60 days—click below to experience comprehensive protection risk-free!
Types of Ransomware FAQs
Q1: Can immutable storage stop all types of ransomware from corrupting my backups?
A1: Yes—immutable storage prevents any modification/deletion after write so even if attackers breach production systems they cannot alter protected backup copies stored this way.
Q2: What should my team do immediately after detecting active encryption activity?
A2: Disconnect affected hosts from networks > Notify incident response team > Preserve forensic evidence > Begin containment/recovery procedures per playbook guidelines > Avoid paying ransoms unless directed by authorities/legal counsel.
Q3: How do I educate staff about recognizing early signs linked with various types of ransomware?
A3: Run quarterly awareness training sessions highlighting phishing red flags/social engineering tricks/unusual system behaviors—and test readiness using simulated email attacks plus tabletop exercises.
Conclusion
Every organization faces risk from multiple types of ransomware—but knowledge plus preparation makes all the difference! By understanding evolving threats—and leveraging robust solutions like Vinchin—you’ll minimize downtime while keeping business-critical data safe no matter what tomorrow brings!
Share on:









