-
Why Encryption Matters in Enterprise Environments
-
How To Choose The Best Red Hat Virtualization Backup Solution for Encryption?
-
Vinchin Backup & Recovery: Enterprise‑Level Backup Solution for Red Hat Virtualization
-
Red Hat Virtualization Backup Software FAQs
-
Conclusion
Which Red Hat Virtualization Backup Solution Offers the Strongest Encryption for Data Security?
Vinchin Backup & Recovery excels by providing strong, end-to-end AES-256 encryption for both data at rest and in transit, centralized key management, and robust access controls. These features ensure enterprise-grade data security, seamless compliance, and operational efficiency, directly addressing the need for maximum backup data protection and regulatory assurance.
Written by Vinchin Solution Team
Protecting data in Red Hat Virtualization (RHV) environments requires more than just regular backups. Strong encryption is now a baseline expectation for any enterprise seeking to defend against cyber threats and comply with strict regulations. The strongest RHV backup solutions use Advanced Encryption Standard (AES) 256-bit encryption both during data transfer and while stored at rest. This approach aligns with recommendations from leading authorities like the National Institute of Standards and Technology, which recognize AES-256 as an industry gold standard for safeguarding sensitive information.
Backup data often becomes a target for attackers because it contains complete copies of critical systems. If left unprotected, this data can expose organizations to ransomware attacks, insider threats, or accidental leaks. Regulatory frameworks such as GDPR, HIPAA, and PCI DSS mandate encrypted backups to ensure privacy and security of personal or financial information. Meeting these requirements is not just about avoiding fines; it is about maintaining customer trust and business continuity.
Encryption transforms readable data into ciphertext that only authorized users can decrypt using secure keys. When implemented correctly across all stages—at rest on storage devices and in transit over networks—it blocks unauthorized access even if physical media are stolen or network traffic is intercepted. For IT teams managing RHV workloads, choosing a backup solution with robust encryption means taking control of risk management while supporting compliance efforts.
Why Encryption Matters in Enterprise Environments
Encryption forms the backbone of modern enterprise security strategies. It shields backup files from prying eyes whether they reside on-premises or in cloud repositories. Organizations today face mounting pressure from regulators, customers, and partners to prove that their sensitive data remains protected at all times.
● Regulatory Compliance
Many industries operate under strict legal frameworks that demand encrypted backups. Regulations like GDPR require organizations to implement “appropriate technical measures” such as strong encryption when processing personal data. Healthcare providers must encrypt patient records under HIPAA guidelines, while retailers handling credit card transactions need to comply with PCI DSS standards.
● Protection Against Data Breaches
Encrypted backups act as a last line of defense if primary systems are compromised. Even if attackers gain access to backup storage locations through malware or phishing campaigns, properly encrypted files remain unreadable without decryption keys.
● Safeguarding Intellectual Property
Enterprises often store proprietary codebases, research findings, or trade secrets within virtual machines managed by RHV clusters. Encrypting these assets ensures competitors cannot exploit them even if physical drives are lost during transport or disposal.
● Mitigating Insider Threats
Not all risks come from outside an organization. Disgruntled employees may attempt unauthorized restores or exfiltrate sensitive archives. Encryption combined with granular access controls limits exposure by ensuring only approved personnel can decrypt backup content.
● Maintaining Customer Trust
Publicized breaches erode confidence quickly—especially when customers learn their private information was left unprotected due to weak security practices. Demonstrating end-to-end encryption reassures stakeholders that your company takes privacy seriously.
In short, robust encryption is not just a checkbox on compliance audits; it is essential for operational resilience in today’s threat landscape.
How To Choose The Best Red Hat Virtualization Backup Solution for Encryption?
Selecting an RHV backup solution involves careful evaluation beyond basic feature checklists. Enterprises should focus on several core criteria that determine how well their chosen tool defends against evolving risks while supporting business growth.
A reliable solution must deliver comprehensive protection without sacrificing usability or scalability:
● End-to-End AES-256 Encryption
Look for platforms offering AES 256-bit encryption both at rest (when stored) and in transit (during network transfers). This level of cryptographic strength meets federal standards set by NIST and provides peace of mind against brute-force attacks.
● Centralized Key Management
Effective key management simplifies compliance reporting and reduces human error risk during audits or disaster recovery scenarios. Centralized tools allow administrators to generate, rotate, revoke, and monitor keys securely from one dashboard rather than relying on scattered manual processes.
● Scalability Across Large Environments
As businesses grow their virtual infrastructure footprint—sometimes spanning hundreds or thousands of VMs—their backup software must scale accordingly without degrading performance or weakening security controls.
● Granular Access Controls
Role-based permissions restrict who can view encrypted backups or initiate restores based on job function rather than blanket administrator rights.
By focusing on these pillars—encryption strength, centralized key management, scalability, and fine-grained access—you ensure your investment delivers lasting value while keeping pace with regulatory demands and organizational change.
Vinchin Backup & Recovery: Enterprise‑Level Backup Solution for Red Hat Virtualization
For enterprises seeking robust protection across Red Hat Virtualization environments—and more than 15 mainstream virtualization platforms including VMware, Hyper-V, Proxmox VE, oVirt/OLVM/RHV clusters—Vinchin Backup & Recovery stands out as a professional-grade VM backup solution built for demanding business needs. Supporting features such as CBT tracking for efficient incremental jobs on RHV/oVirt/OLVM clusters; LAN-free backup options; instant recovery capabilities; advanced scheduling; plus full support for AES‑256 encryption at rest/in transit—this platform delivers comprehensive coverage tailored to large-scale deployments.
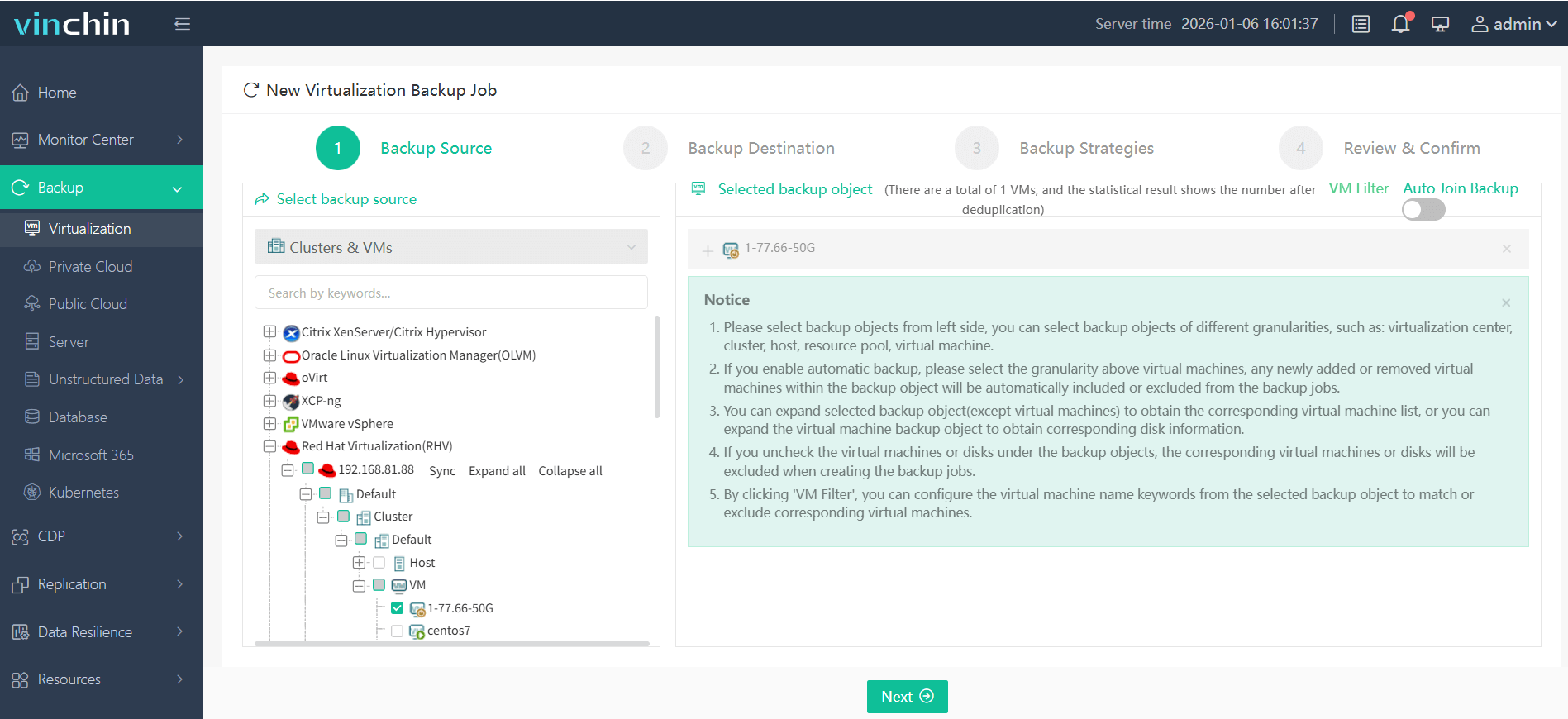
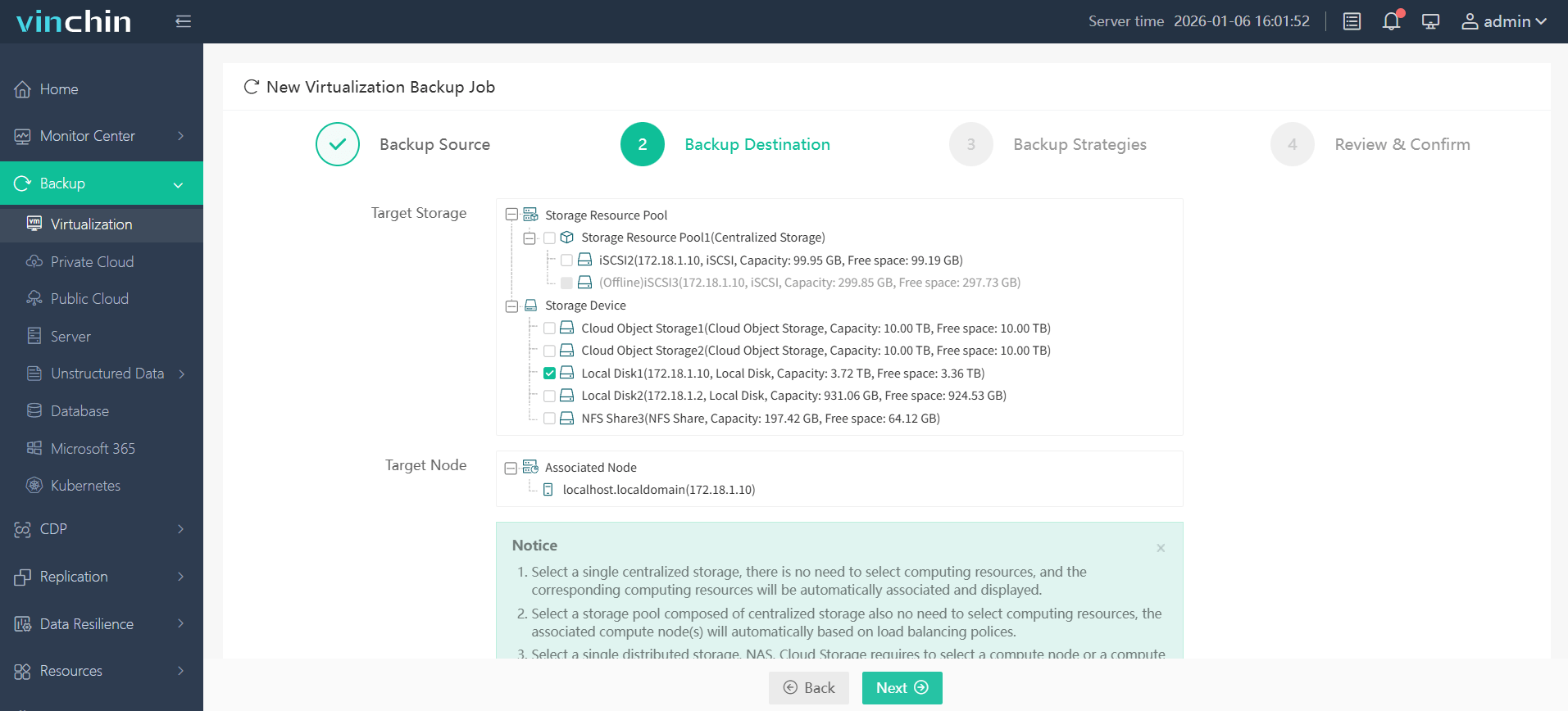
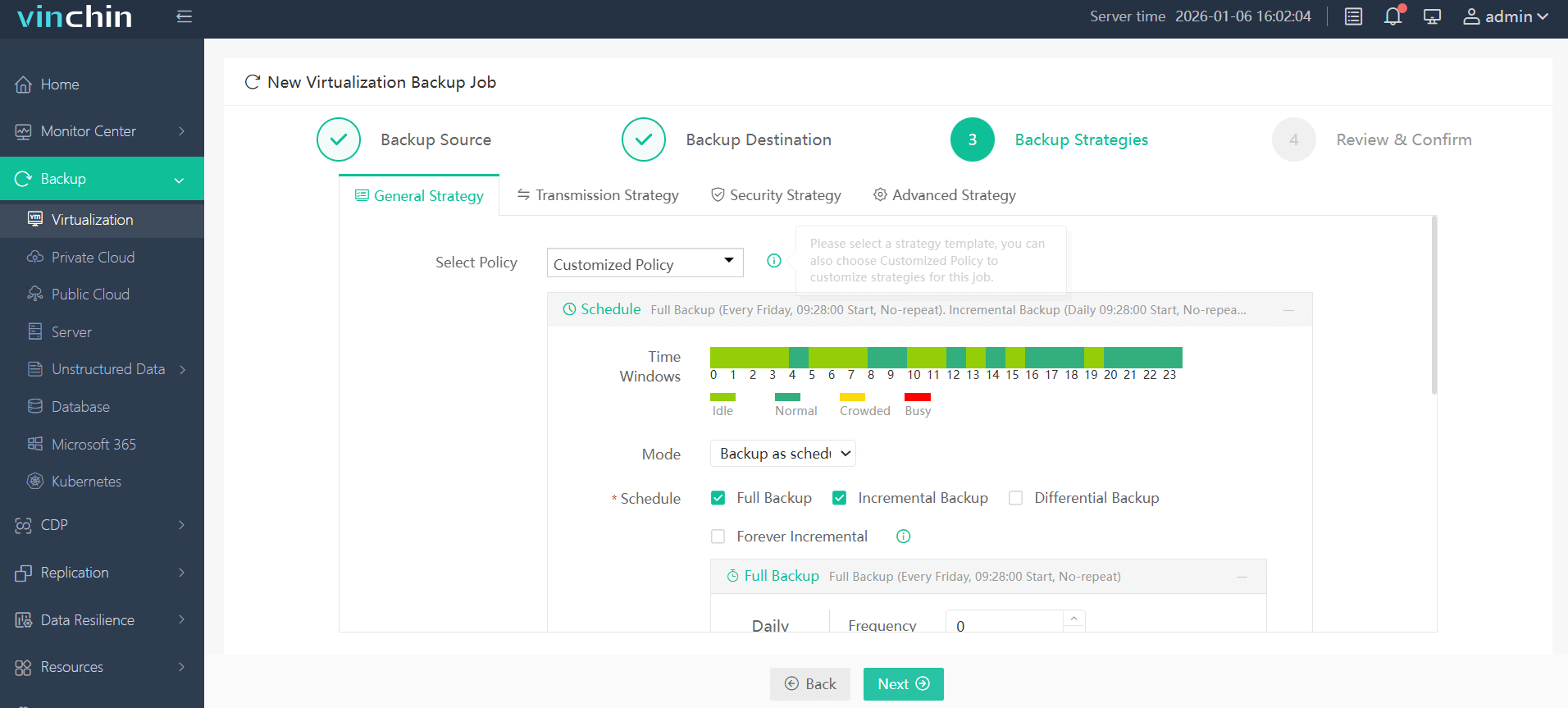
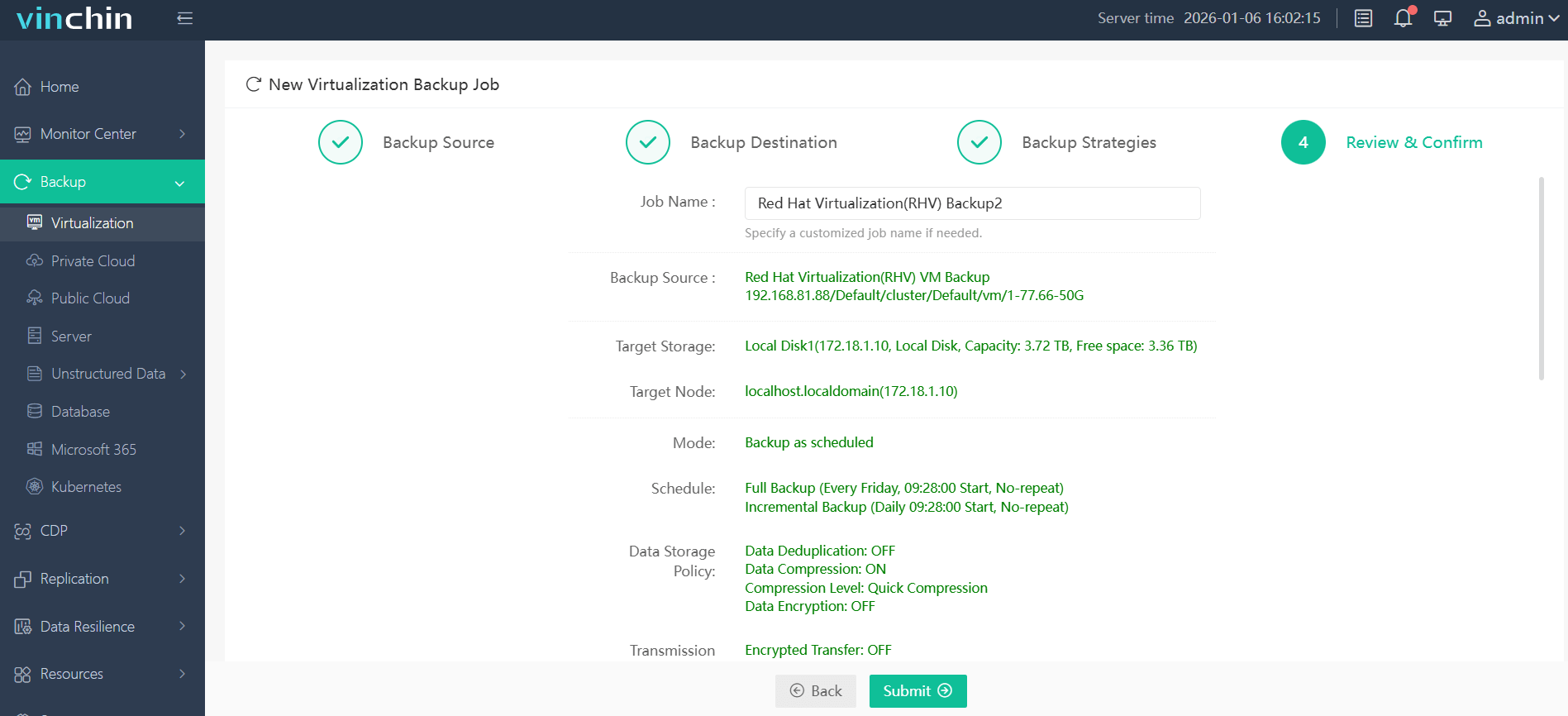
With Vinchin Backup & Recovery’s intuitive web console interface:
Step 1: Select the RHV VM you wish to back up.
Step 2: Choose your preferred backup storage location.
Step 3: Configure your desired backup strategy—including schedule/frequency/encryption settings.
Step 4: Submit the job.
Recognized globally among enterprise IT teams—with top ratings from thousands of satisfied customers—Vinchin Backup & Recovery offers a fully featured free trial valid for 60 days so you can evaluate its benefits firsthand.
Red Hat Virtualization Backup Software FAQs
Q1: Does strong encryption impact backup performance?
Modern solutions use optimized algorithms—including hardware acceleration—to minimize any slowdown caused by encrypting large datasets during transfer or storage operations.
Q2: Is key management included?
Yes; enterprise-grade software provides centralized dashboards so administrators can manage keys efficiently throughout their lifecycle—from creation through rotation—with full audit trails available for compliance checks at any time.
Q3: Can encrypted backups be made immutable?
Absolutely; leading platforms combine strong cryptography with immutability settings so archived copies cannot be altered—even accidentally—or deleted until retention periods expire according to policy rules set within administrative consoles.
Q4: Are all backup types supported with full encryption?
Comprehensive solutions apply end-to-end protection automatically whether running full image jobs covering entire virtual machines—or incremental/differential tasks capturing daily changes—to guarantee consistent coverage across every workload managed inside RHV clusters.
Conclusion
Choosing robust AES‑256 encrypted backups protects your organization’s RHV environment against threats while supporting regulatory compliance goals efficiently.
Share on:








