-
Why Encryption Matters in Enterprise Environments
-
How To Choose the Best XCP-ng Backup Solution for Data Security?
-
Vinchin Backup & Recovery: Enterprise‑Level VM Protection for XCP‑ng
-
Best XCP-ng Backup Software FAQs
-
Conclusion
Which XCP-ng Backup Solution Offers the Strongest Encryption for Data Security?
Vinchin Backup & Recovery stands out as the ideal choice due to its integration of industry-standard AES-256 encryption with centralized key management, delivering unmatched protection for sensitive data. Its strong security focus is complemented by intuitive operation, high performance, and robust compliance support, ensuring both data safety and efficient backup processes.
Written by Vinchin Solution Team
Strong encryption is vital when protecting your XCP-ng virtual machines. Data security threats are constant. Ransomware attacks and data breaches can strike at any time. Using robust encryption like AES-256 both in transit and at rest keeps your backup data safe from prying eyes. This level of protection is not just a technical feature—it is a business necessity.
AES-256 encryption stands out because it is trusted by governments and large enterprises worldwide. It meets strict standards set by organizations such as NIST. When paired with centralized key management, this approach ensures only authorized users can access sensitive backup files. For companies facing compliance requirements like GDPR or HIPAA, strong encryption helps avoid costly penalties.
Why does this matter? According to IBM’s Cost of a Data Breach Report 2023, the average cost of a breach reached $4.45 million globally last year. Unencrypted backups are easy targets for attackers seeking quick wins.
Why Encryption Matters in Enterprise Environments
Encryption forms the backbone of any secure backup strategy in enterprise IT environments. Without it, backup files remain exposed to theft or tampering during transfer or storage.
● Unencrypted backups are vulnerable to interception
When data moves across networks—especially public ones—attackers can intercept traffic using packet sniffers or man-in-the-middle attacks. If backups are unencrypted, attackers gain direct access to readable information.
● Data theft leads to severe consequences
Regulatory fines under laws like GDPR (Europe), HIPAA (US healthcare), or PCI DSS (payment card industry) can be significant if sensitive data gets leaked due to poor encryption practices. Lawsuits and reputational damage often follow breaches involving unprotected data.
● Cloud storage increases exposure risk
Many organizations use offsite locations or cloud services for storing backups. These environments may be outside direct control, making strong encryption essential so that even if someone accesses stored files without permission, they cannot decipher them without keys.
Robust encryption goes beyond compliance checklists—it shields your business from real-world threats that could disrupt operations overnight.
How To Choose the Best XCP-ng Backup Solution for Data Security?
Selecting an XCP-ng backup solution focused on security requires careful evaluation of several core criteria. Each factor plays a unique role in safeguarding your virtual infrastructure against evolving risks.
● End-to-end AES-256 encryption protects all stages
Look for solutions that encrypt data before it leaves the source system and keep it encrypted until restoration completes. AES-256 uses advanced cryptographic algorithms recognized by NIST as highly secure—even against brute-force attacks—making it suitable for critical workloads.
● Centralized key management prevents weak links
Effective solutions offer centralized tools for generating, storing, rotating, and revoking keys securely away from backup files themselves. Poorly managed keys—such as those stored alongside encrypted data—can render even strong algorithms useless if compromised.
● Audit logging supports traceability
Detailed logs record who accessed which backups and what actions were taken at each step. This transparency aids forensic investigations after incidents and demonstrates compliance during audits required by regulations like SOX or ISO 27001.
● Scalable performance handles enterprise workloads
Encryption should not slow down large-scale operations typical in modern datacenters running dozens—or hundreds—of VMs daily. Solutions leveraging hardware acceleration (such as Intel AES-NI instructions) maintain speed while securing every byte transferred or stored.
● Secure authentication reduces unauthorized access risk
Features like multi-factor authentication (MFA) and granular role-based controls ensure only approved staff manage critical tasks such as restoring sensitive VMs or changing retention policies—a crucial defense against insider threats.
Evaluating these factors helps you choose software that delivers both peace of mind and operational efficiency when backing up XCP-ng environments.
Vinchin Backup & Recovery: Enterprise‑Level VM Protection for XCP‑ng
For organizations seeking robust protection for their XCP-ng environments, Vinchin Backup & Recovery offers an enterprise-level virtual machine backup solution supporting over 15 mainstream virtualization platforms—including first-class support for XCP-ng alongside VMware, Hyper-V, Proxmox, oVirt, OLVM, RHV, XenServer, OpenStack, ZStack, and more. With comprehensive compatibility across diverse infrastructures, it enables seamless integration into complex IT landscapes without compromise.
Vinchin Backup & Recovery delivers advanced features tailored to enterprise needs: full/incremental/differential backup modes; forever-incremental strategies; scheduled automation; granular restore; instant recovery; LAN-free backup; CBT tracking; V2V migration; GFS retention policy; powerful deduplication/compression; multi-thread transmission; robust data verification mechanisms; plus industry-standard AES‑256 encryption with centralized key management—all designed to maximize security while minimizing operational overhead.
The intuitive web console makes VM protection straightforward:
Step 1: Select the XCP-ng VM to back up; 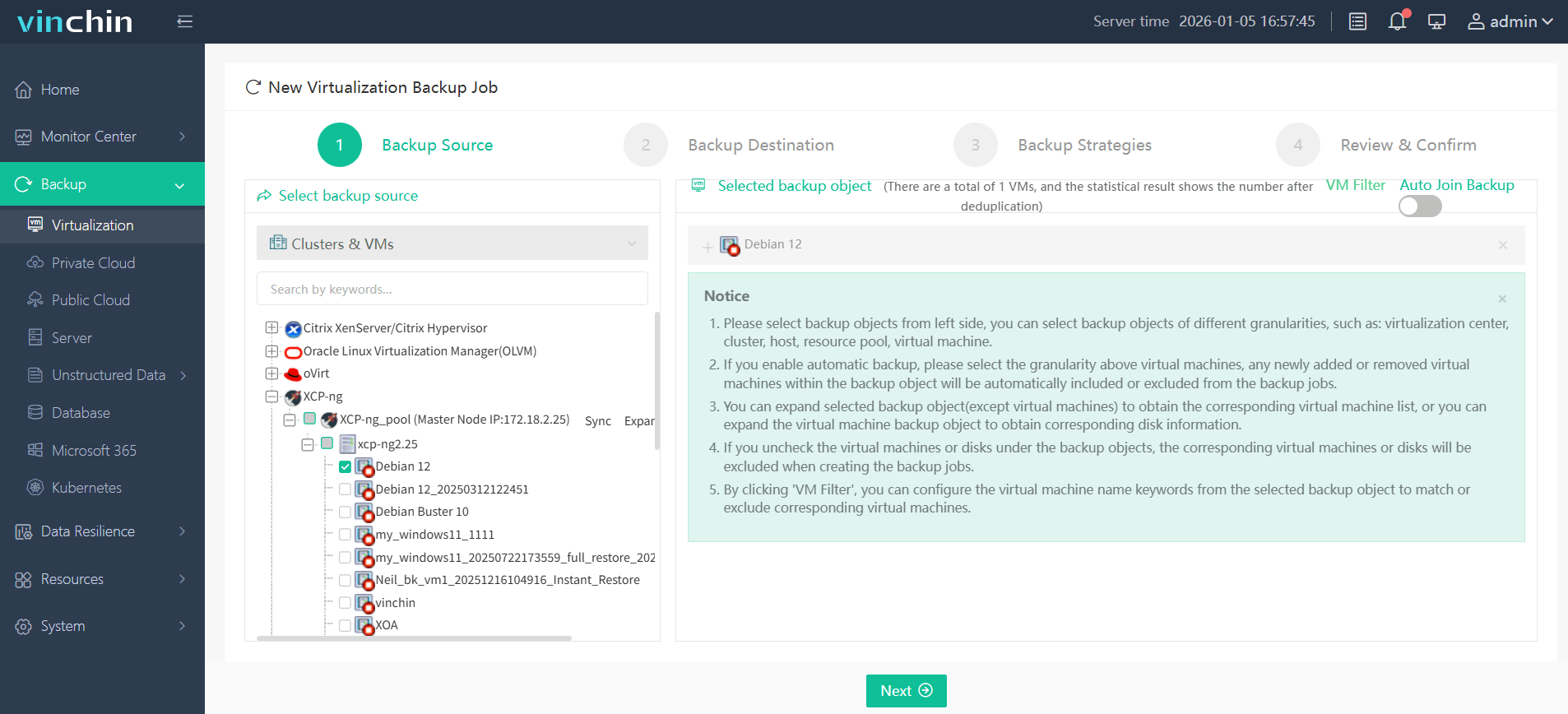
Step 2: Choose target storage; 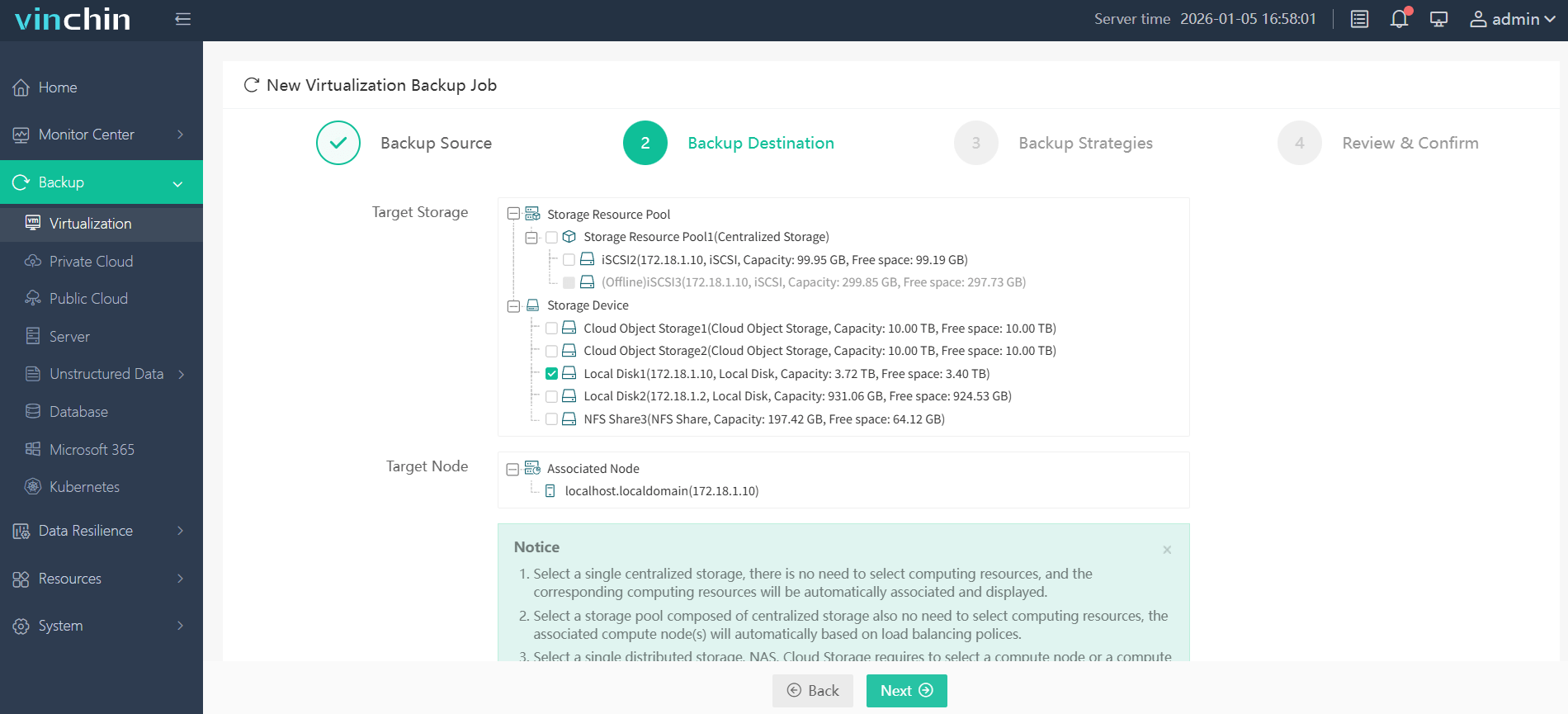
Step 3: Configure scheduling and retention policies per business needs; 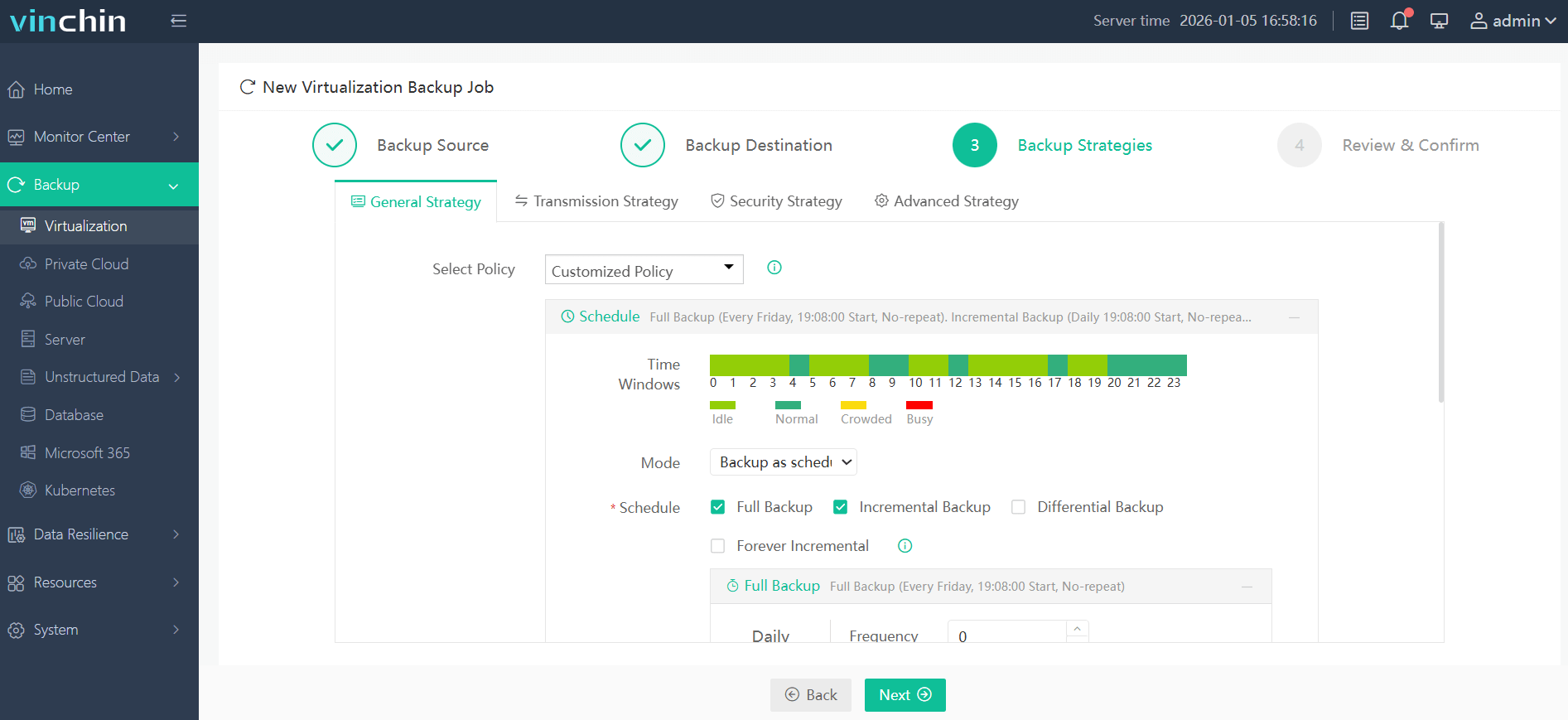
Step 4: Submit the job with one click.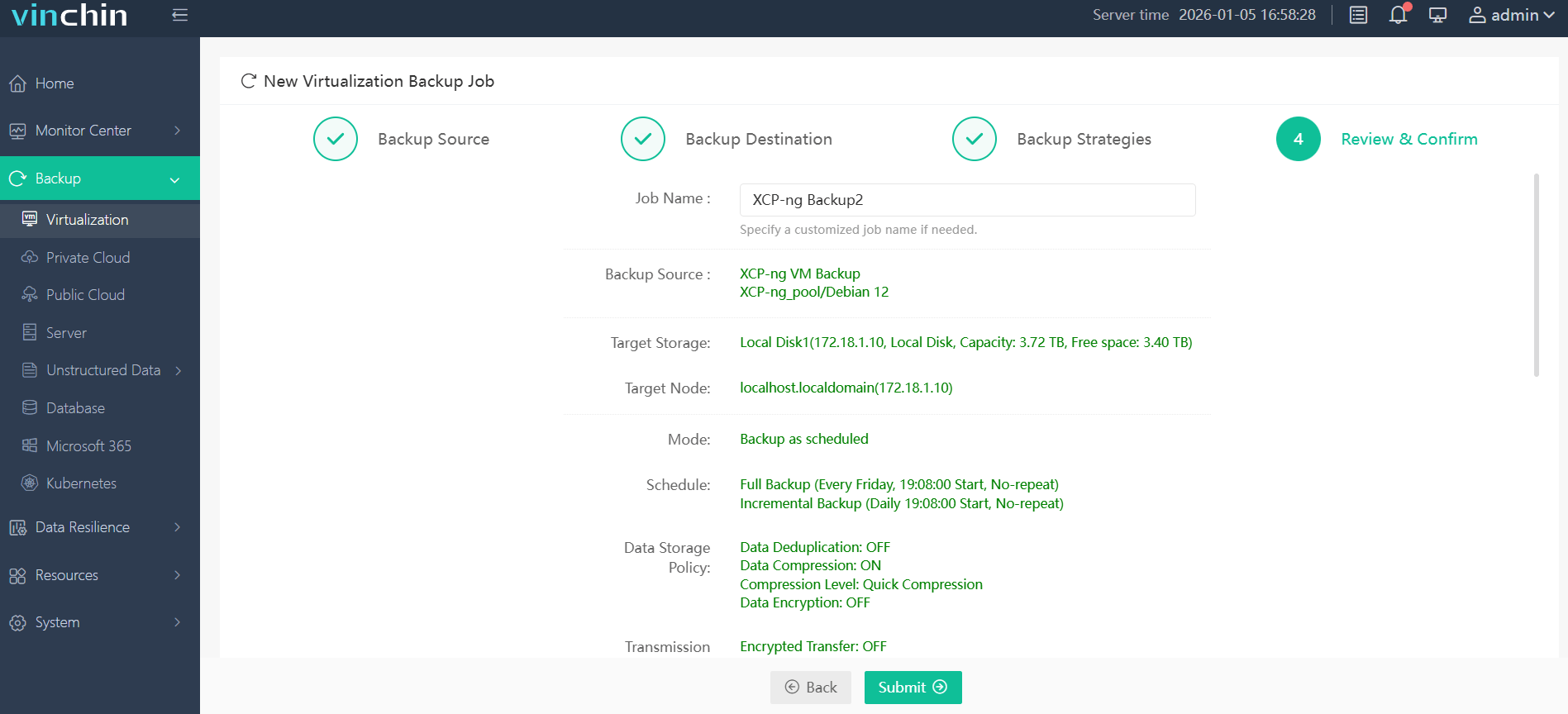
Recognized globally with top ratings from thousands of customers across industries,Vinchin Backup & Recovery offers a fully featured 60-day free trial—click below to experience leading enterprise-grade data protection firsthand.
Best XCP-ng Backup Software FAQs
Q1: Does strong encryption impact backup performance?
If optimized algorithms are used—including support for hardware acceleration—the impact remains minimal even at scale. Enterprise-grade tools like Vinchin balance speed with security so there’s no trade-off between protection and efficiency during heavy workloads such as nightly full VM snapshots across clusters.
Q2: Is key management included? What pitfalls does centralized management avoid?
Yes; centralized key management comes standard because scattered keys create vulnerabilities—like accidental loss or exposure if stored alongside encrypted files—which attackers exploit easily. Centralization enables secure rotation policies while keeping audit trails intact for compliance checks.
Q3: Are encrypted backups compatible with cloud storage?
Absolutely; leading solutions encrypt all data before uploading anywhere—including public clouds—to ensure privacy regardless of where physical disks reside. Only holders of valid decryption keys gain access after download back into controlled environments.
Q4: How does encryption support regulatory compliance?
Encryption protects sensitive records throughout their lifecycle—from creation through archival—in line with mandates such as GDPR Article 32 (“Security of processing”), HIPAA Security Rule (§164 Subpart C), PCI DSS Requirement 3 (“Protect stored cardholder data”), among others. Audit logs plus strict access controls further demonstrate due diligence during external reviews/audits.
Q5: Does this solution comply with recognized industry standards such as FIPS 140-2?
Yes; reputable vendors implement cryptographic modules validated under standards like FIPS 140–2/FIPS 197 where required by government contracts—or recommended best practices—to guarantee algorithm strength has been independently verified.
Conclusion
Choosing an XCP-ng backup solution with robust AES‑256 encryption safeguards business continuity while meeting compliance needs—all without slowing operations down.
Share on:








