-
Why Data Encryption Matters in Enterprise Environments
-
How To Choose The Best Oracle OLVM Backup Solution for Data Encryption?
-
Vinchin Backup & Recovery: Enterprise-Level VM Protection Across Platforms
-
Best Oracle OLVM Backup Software FAQs
-
Conclusion
Which Oracle OLVM Backup Solution Offers the Strongest Encryption for Data Security?
Vinchin Backup & Recovery stands out as the top choice for organizations requiring the strongest data security through robust encryption. Its end-to-end AES-256 encryption ensures data remains protected both in transit and at rest, supporting strict compliance standards. Combined with centralized key management, high scalability, and minimal impact on performance, it effectively safeguards sensitive information.
Written by Vinchin Solution Team
Encryption is essential when protecting your Oracle Linux Virtualization Manager (OLVM) environment. Modern threats target backup data as much as production systems. The strongest Oracle OLVM backup solutions use end-to-end AES-256 encryption—recognized by organizations like NIST as a gold standard for data protection. This level of security keeps your backups safe from unauthorized access during storage or transfer.
Organizations running sensitive workloads or facing strict regulations cannot afford weak protection. Encryption helps you avoid costly breaches and supports business continuity even if attackers breach other defenses. Regulatory demands such as GDPR or HIPAA require encrypted storage and transmission of sensitive information. Choosing a backup solution with proven encryption is now a basic requirement for enterprise risk management.
Why Data Encryption Matters in Enterprise Environments
Data encryption forms the backbone of secure backup strategies in any enterprise setting. It ensures that even if someone intercepts or steals your backup files, they cannot read or misuse your data without proper authorization.
● Prevents Unauthorized Access: Without strong encryption, backups become easy targets for attackers or insiders who may exploit unprotected files. For example, ransomware groups often search specifically for unencrypted backups to maximize leverage during attacks.
● Reduces Regulatory Risk: Many industries must comply with laws like GDPR, HIPAA, PCI DSS, or SOX that mandate encrypted storage of personal or financial data. Failing to encrypt can result in heavy fines and legal action if a breach occurs.
● Protects Reputation: A single incident involving exposed backup data can damage customer trust permanently. Publicized breaches often involve lost tapes or stolen disks containing unencrypted archives—events that could have been avoided with robust encryption policies.
● Supports Secure Cloud Adoption: As more organizations move backups offsite or into cloud environments, encryption becomes vital to prevent exposure during transit over public networks or while stored on third-party infrastructure.
Encryption transforms readable information into ciphertext using algorithms like AES (Advanced Encryption Standard). AES-256 uses a 256-bit key length—making brute-force attacks virtually impossible with current technology. Even if someone obtains an encrypted file without its key, it remains useless to them.
How To Choose The Best Oracle OLVM Backup Solution for Data Encryption?
Selecting an effective backup solution means looking beyond surface features to ensure comprehensive security at every stage of your workflow. Here’s what matters most:
A well-chosen solution should provide both robust protection and operational efficiency as your environment grows.
● Industry-standard AES-256 Encryption: Always confirm that the software uses AES-256 encryption for both data at rest (when stored) and in transit (while moving across networks). This dual-layer approach ensures no gap exists where attackers might intercept readable information. Some solutions may also offer options like FIPS-compliant modules for government-grade security requirements.
● Centralized Key Management: Effective key management reduces human error risks by controlling who can access decryption keys from one place. Look for support of hardware security modules (HSMs), automated key rotation policies, audit trails of key usage events, and integration with existing identity management systems such as LDAP or Active Directory.
● Compliance Certifications: Solutions aligned with standards like ISO 27001, SOC 2 Type II, GDPR Article 32, HIPAA Security Rule §164.312(a)(2)(iv), or PCI DSS Requirement 3 help you pass audits more easily while reducing regulatory exposure. Documentation showing regular third-party audits adds further confidence in vendor claims about their controls.
● Scalability Without Performance Loss: As virtual machine counts grow into hundreds or thousands across multiple sites—or when storing petabytes of historical backups—encryption should not slow down operations noticeably. Advanced solutions use parallel processing engines and hardware acceleration (such as Intel AES-NI instructions) so you maintain fast backup windows even under heavy loads.
● Seamless Integration With Existing Infrastructure: The best tools work smoothly alongside your current authentication systems and network segmentation rules without requiring major changes to firewall settings or user permissions structures—a critical factor in large-scale deployments where complexity increases risk of misconfiguration leading to accidental exposures.
By focusing on these areas when evaluating products—and asking vendors how they address each point—you build a foundation that protects both business continuity goals and compliance mandates long-term.
Vinchin Backup & Recovery: Enterprise-Level VM Protection Across Platforms
For enterprises seeking advanced protection for Oracle OLVM environments, Vinchin Backup & Recovery delivers professional-grade VM backup capabilities supporting over 15 mainstream virtualization platforms—including VMware, Hyper-V, Proxmox, oVirt, RHV, XCP-ng, XenServer, OpenStack, ZStack—and prominently Oracle OLVM itself. Vinchin Backup & Recovery offers agentless operation and centralized management through an intuitive web console designed for scalability across diverse infrastructures.
Key features include incremental backup leveraging CBT technology on supported platforms; LAN-free backup; granular restore; V2V migration; scheduled policy-driven jobs; plus robust deduplication and compression—all engineered to optimize performance while minimizing resource consumption. These functions collectively enhance reliability and efficiency while ensuring compliance with stringent enterprise requirements.
To back up an Oracle OLVM VM using Vinchin Backup & Recovery is straightforward:
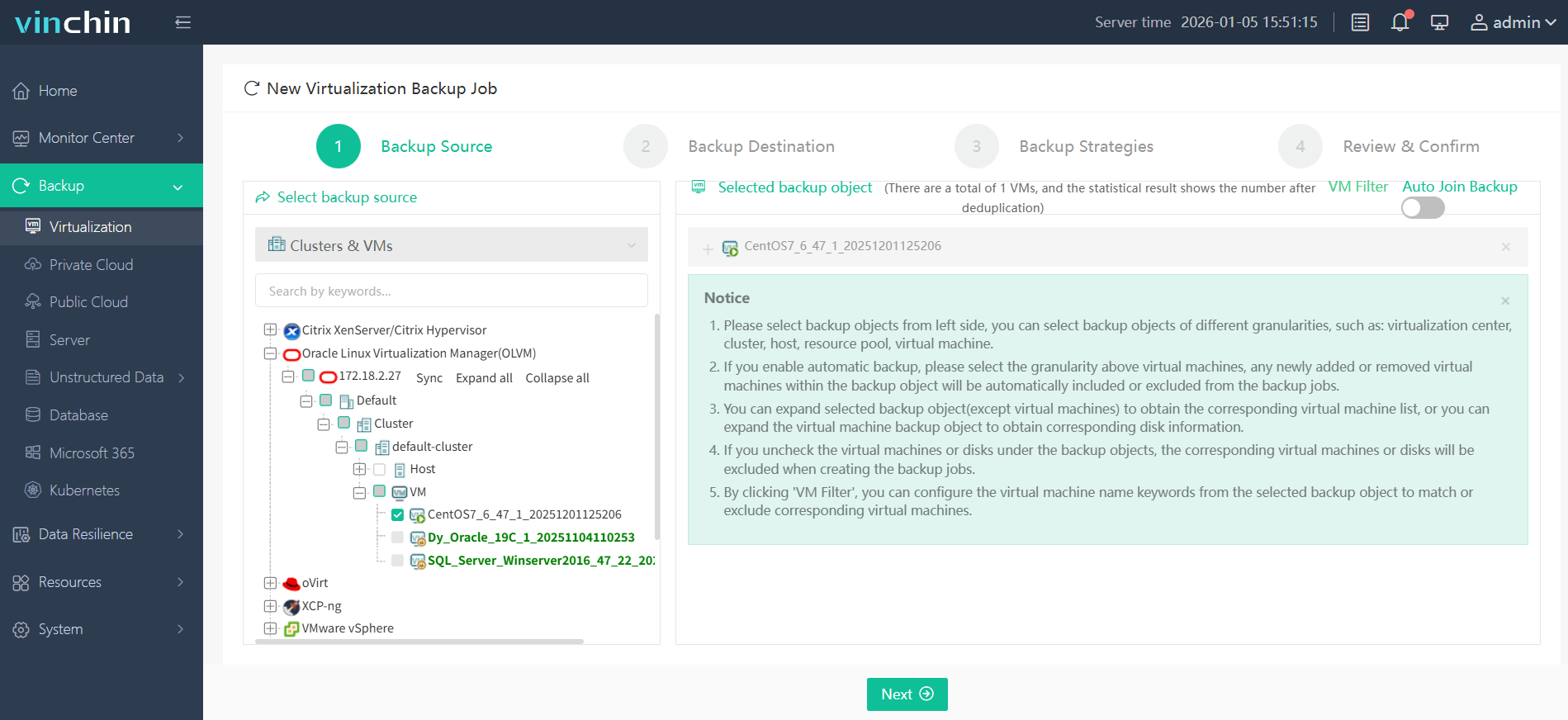
Step 1: Select the Oracle OLVM VM to back up;
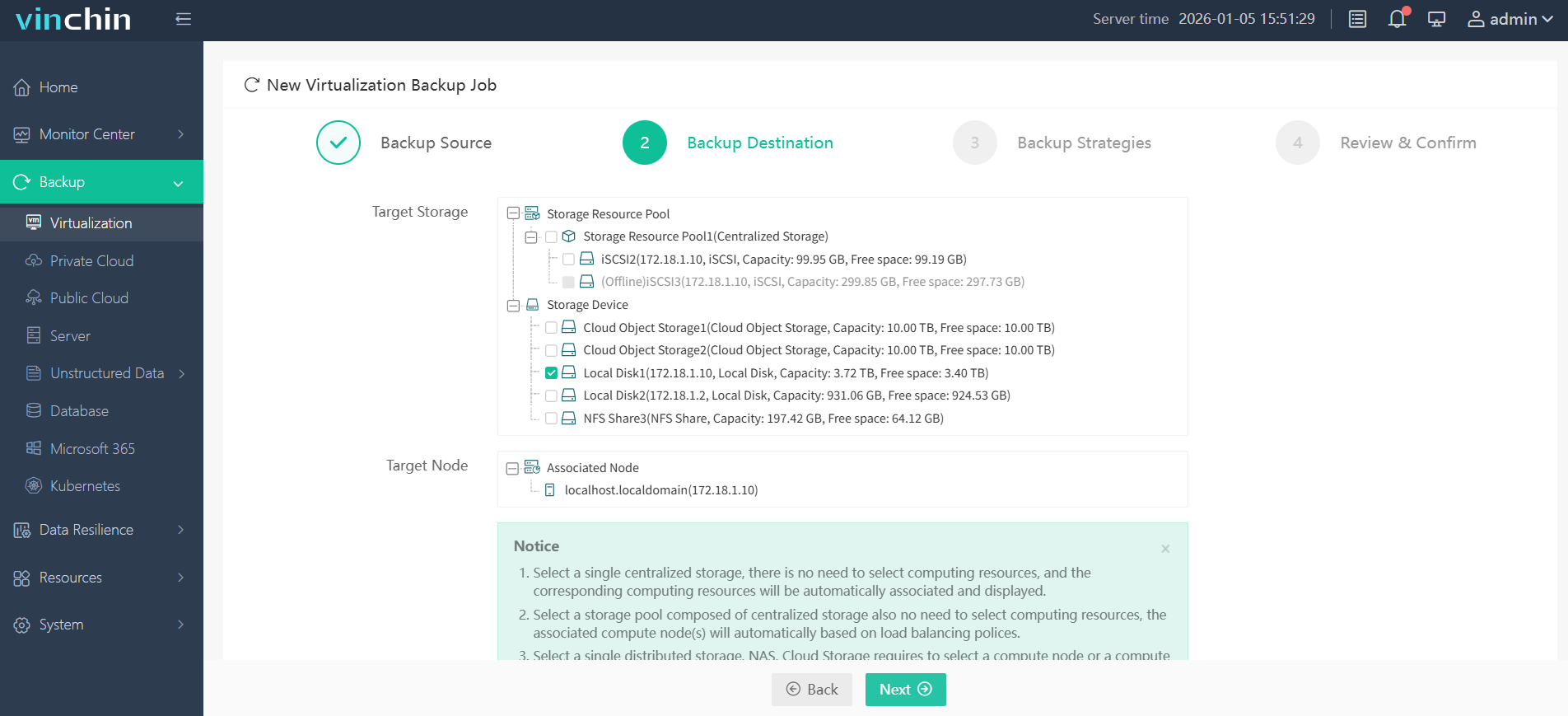
Step 2: Choose the desired backup storage;
Step 3: Configure the appropriate strategy (including scheduling and retention);

Step 4: Submit the job via the streamlined web interface.

Recognized globally by thousands of customers with top ratings in enterprise data protection software reviews—Vinchin Backup & Recovery offers a full-featured free trial valid for 60 days so you can evaluate its capabilities firsthand.
Best Oracle OLVM Backup Software FAQs
Q1: Does the solution encrypt both backup data in transit and at rest?
Yes. Leading solutions—including Vinchin Backup & Recovery—use industry-standard AES-256 encryption at every stage: while transferring files across networks (“in transit”) as well as when storing them locally or offsite (“at rest”). This layered approach maximizes protection against interception by hackers during transfer or theft from physical media after storage
Q2: How does key management impact security?
Centralized key management plays a crucial role by limiting who can generate—or recover—decryption keys through strict access controls tied into corporate identity systems like LDAP/Active Directory integration or Hardware Security Modules (HSMs). Automated processes such as scheduled key rotation reduce manual errors while audit logs track every operation involving sensitive keys so you meet compliance requirements efficiently.
Q3: Is there an impact on performance when using strong encryption?
Enterprise-grade solutions minimize performance loss through optimizations such as parallel processing engines that split tasks among CPU cores plus hardware acceleration technologies like Intel’s AES-NI instruction set found on modern processors. These advances allow full-strength AES–256 protection without slowing down daily operations—even at scale.
Q4: Are these solutions compliant with major regulations?
Top-tier products enforce strong default policies aligned with global standards including GDPR Article 32 requirements around “state-of-the-art” cryptography; HIPAA Security Rule mandates; PCI DSS rules covering cardholder info; ISO 27001 controls; SOC2 Type II reporting; plus regular third-party audits verifying ongoing adherence—all supporting successful regulatory reviews.
Conclusion
Choose an Oracle OLVM backup solution with proven AES‑256 encryption to ensure true security and compliance at scale—without sacrificing speed or flexibility along the way.
Share on:








